Imagine this, you're chilling at home, sipping your favorite coffee, and suddenly you realize you need to access your IoT devices that are connected through a Raspberry Pi. No worries, my friend, because with the right remote IoT platform SSH key setup, you can do that from anywhere in the world! This isn't just about convenience; it's about taking control of your tech life, whether you're a hobbyist or a professional developer. Let's dive into how you can harness the full potential of remote IoT platforms using SSH keys on a Raspberry Pi.
Now, before we get into the nitty-gritty details, let's talk about why this is such a big deal. The Internet of Things (IoT) has revolutionized the way we interact with technology, and Raspberry Pi has become a go-to device for enthusiasts and professionals alike. By setting up a secure remote access system, you're not only ensuring your data stays safe but also giving yourself the flexibility to manage your projects from anywhere. Who wouldn’t want that, right?
But here's the thing, setting up remote access isn’t as simple as flipping a switch. You need to understand the ins and outs of SSH keys, how they work, and how to configure them properly on your Raspberry Pi. This article is your ultimate guide to doing just that. So, grab your favorite snack, and let's get started!
Read also:Blake Shelton And Gwen Stefani Set To Light Up The Grammy Stage
Table of Contents:
- Introduction to Remote IoT Platforms
- Understanding SSH Basics
- Raspberry Pi Setup
- Generating SSH Keys
- Securing Your SSH Connection
- Troubleshooting Common Issues
- IoT Applications Using SSH
- Best Practices for Remote IoT
- Future Trends in IoT Platforms
- Conclusion and Next Steps
Introduction to Remote IoT Platforms
So, what exactly is a remote IoT platform? Think of it as a bridge that connects all your smart devices, allowing you to manage and monitor them from anywhere. Whether you're controlling smart home devices, monitoring industrial equipment, or running a weather station, a remote IoT platform gives you the power to do it all without being physically present.
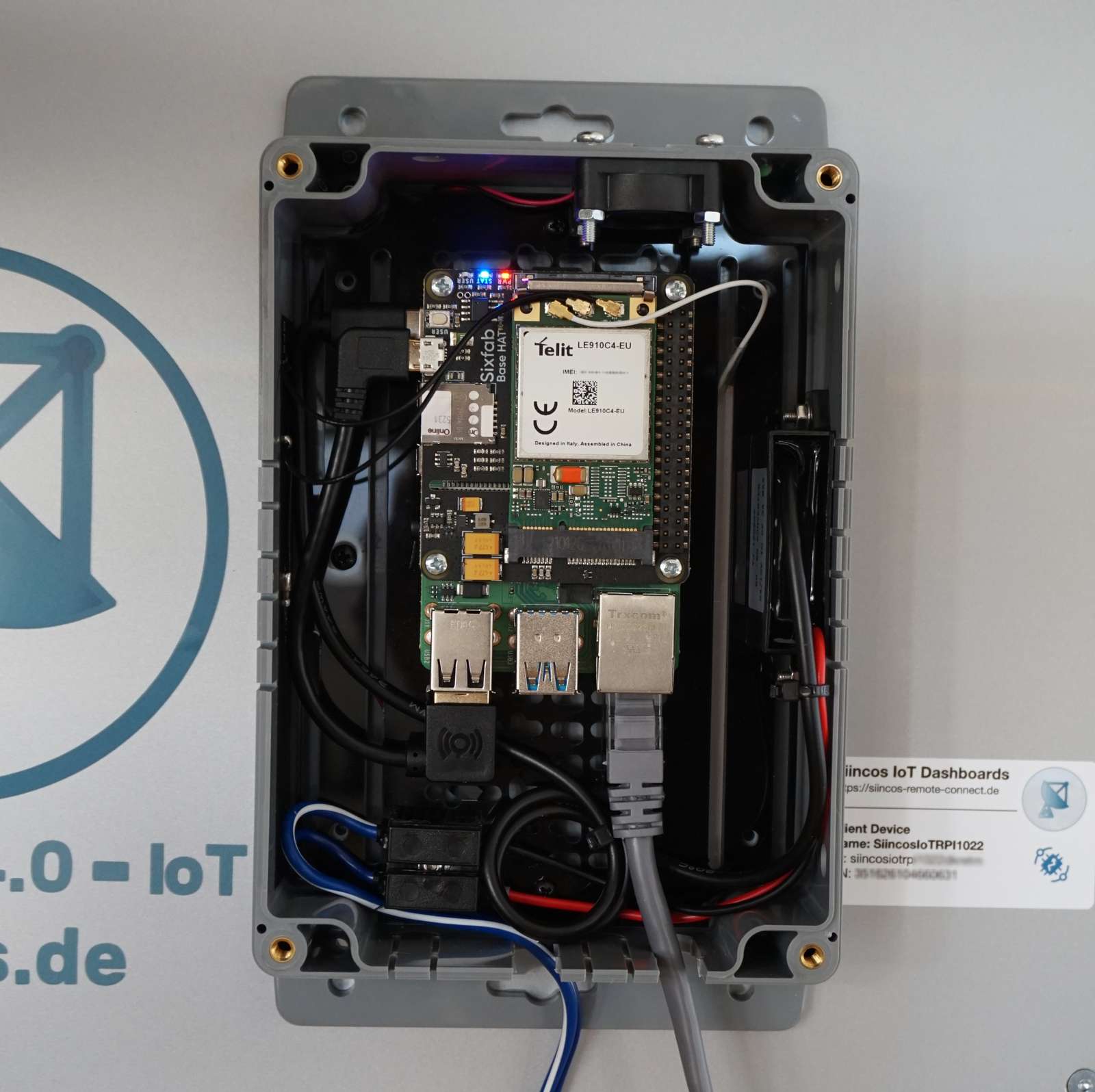
Why Choose Raspberry Pi?
Raspberry Pi is like the Swiss Army knife of the tech world. It’s affordable, versatile, and packed with features that make it perfect for IoT projects. Plus, its compatibility with Linux makes it a dream to work with when setting up SSH connections. You can turn this tiny device into a powerhouse for managing your IoT ecosystem.
Understanding SSH Basics
SSH, or Secure Shell, is the backbone of secure remote connections. It’s like a secret tunnel that lets you access your devices without anyone else peeking in. SSH keys add an extra layer of security by using a pair of cryptographic keys – a public key and a private key – to authenticate your identity.
How SSH Works
Here's a quick rundown of how SSH works: When you try to connect to a remote device, your public key is sent to the server. If the server recognizes your public key, it allows you access. The private key, which stays on your local machine, is the key to unlocking this connection. It’s like having a secret handshake with your Raspberry Pi!
Raspberry Pi Setup
Before you can start using SSH, you need to set up your Raspberry Pi properly. This involves installing the necessary software, configuring the network settings, and enabling SSH.
Read also:Gisele Buumlndchen Tom Brady And Their Sweet Indulgence
Step-by-Step Raspberry Pi Setup
- Install the latest version of Raspberry Pi OS on your device.
- Connect your Raspberry Pi to your local network using Wi-Fi or Ethernet.
- Enable SSH by navigating to the Raspberry Pi Configuration menu and ticking the SSH option.
- Set up a static IP address to ensure your Raspberry Pi always has the same network address.
Generating SSH Keys
Now that your Raspberry Pi is ready, it's time to generate those SSH keys. This is where the magic happens. You’ll need to create a pair of keys – one public and one private – and then copy the public key to your Raspberry Pi.
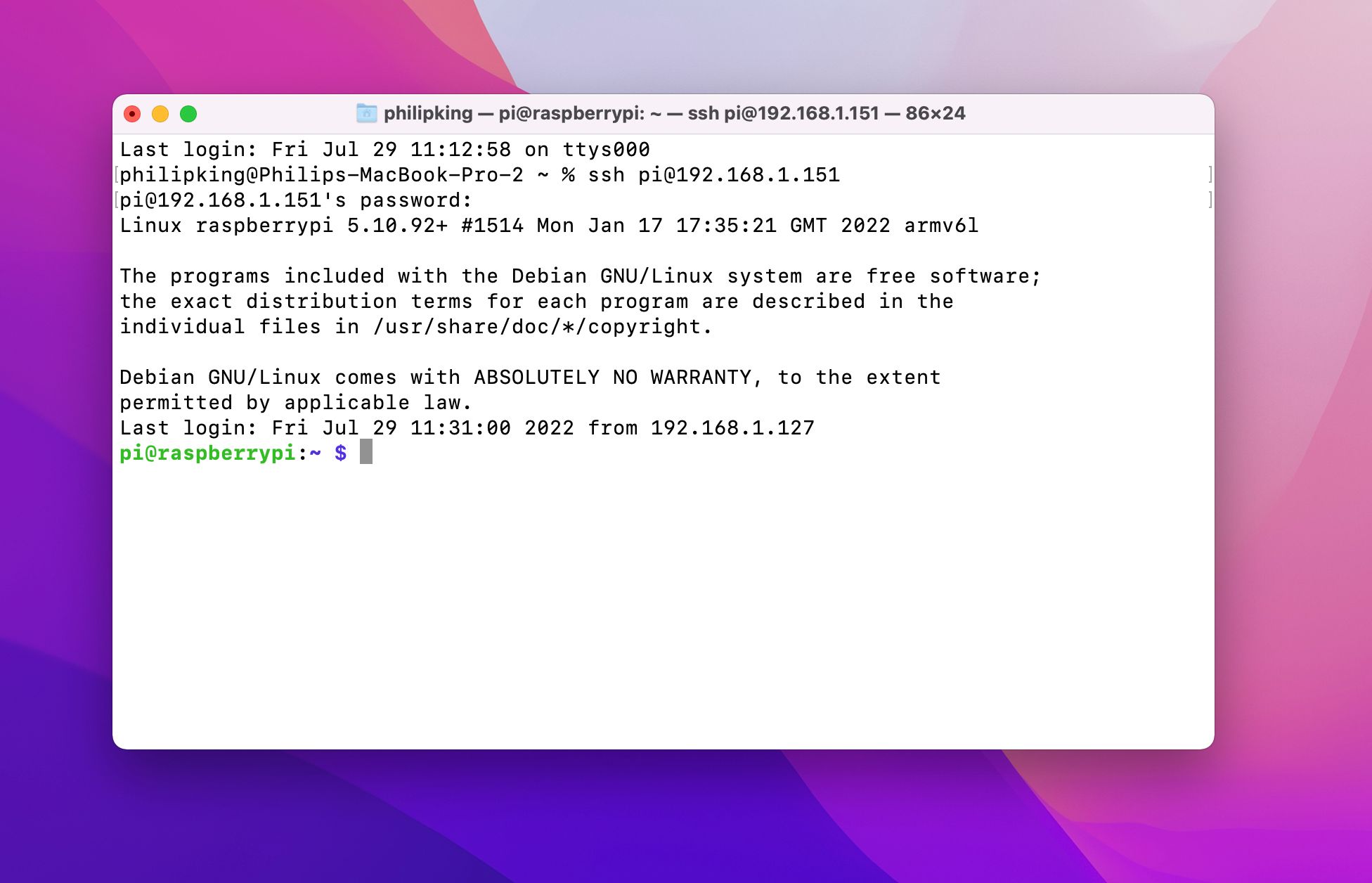
Generating Keys on Linux/Mac
On a Linux or Mac machine, open up your terminal and type the following command:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com"
This will generate a new RSA key pair with a length of 4096 bits. Make sure to save your keys in a secure location and remember the passphrase you set!
Copying the Public Key
Once you’ve generated your keys, you need to copy the public key to your Raspberry Pi. You can do this using the ssh-copy-id command:
ssh-copy-id pi@your_raspberry_pi_ip
And just like that, your Raspberry Pi is ready to accept secure SSH connections!
Securing Your SSH Connection
Security should always be at the forefront of your mind when setting up remote access. While SSH keys provide a strong layer of protection, there are additional steps you can take to secure your connection even further.
Best Security Practices
- Disable password authentication and rely solely on SSH keys.
- Change the default SSH port from 22 to something less common to deter automated attacks.
- Use a firewall to limit access to your SSH port only from trusted IP addresses.
- Regularly update your Raspberry Pi OS and SSH software to patch any security vulnerabilities.
Troubleshooting Common Issues
Even with the best setup, things can go wrong. Here are some common issues you might encounter and how to fix them.
Connection Refused
If you’re getting a "connection refused" error, double-check that SSH is enabled on your Raspberry Pi and that your firewall isn’t blocking the SSH port. Also, ensure that your IP address hasn’t changed if you’re using a dynamic IP.
IoT Applications Using SSH
Now that you’ve got your Raspberry Pi all set up with SSH, it’s time to explore some cool IoT applications you can build. From home automation systems to environmental monitoring stations, the possibilities are endless.
Home Automation
Use your Raspberry Pi to control smart lights, thermostats, and security systems from anywhere. With SSH, you can manage these devices securely without worrying about unauthorized access.
Best Practices for Remote IoT
To get the most out of your remote IoT platform, follow these best practices:
- Always use strong, unique passwords for all your devices.
- Regularly back up your data to prevent loss in case of hardware failure.
- Keep your software up to date to benefit from the latest features and security patches.
Future Trends in IoT Platforms
The world of IoT is evolving rapidly, and new trends are emerging all the time. Edge computing, AI integration, and enhanced security measures are just a few of the exciting developments on the horizon. Staying informed about these trends will help you stay ahead of the curve and make the most of your IoT projects.
Conclusion and Next Steps
Setting up a remote IoT platform with SSH keys on a Raspberry Pi might seem daunting at first, but with the right guidance, it’s totally doable. You’ve now got all the tools and knowledge you need to create a secure, flexible system that lets you manage your IoT devices from anywhere in the world.
So, what’s next? Start by experimenting with your Raspberry Pi and see what cool projects you can come up with. Share your experiences and creations with the community, and don’t forget to leave a comment below if you have any questions or need further assistance. Happy tinkering, and see you in the next article!